Assessment & Strategy
- Document assets and dependencies in a single pane of glass, whether on premises or in the public or private cloud.
- Application(s) Migration Assessment
- Infrastructure Assessment
- Cloud Strategy
Plan & Act
- Cloud migration management
- DevOps Services
- Cloud migration Services
- Cloud Application testing & go live
Infrastructure Planning
- Network
- Connectivity to Corporate Network
- VPC
- DNS
- Authentication
- Corporate users authentication to cloud services
- Computing Capacity
- Storage Capacity
Cloud Management and Operations
- Cloud Operations
- Security Operations
- Application Management
- Analytics
Socialization / Maximize the value
- Identify SMEs
- Train the trainer
- Culture Evolution
Cloud Cost Control & Security
- To forecast AWS, Azure, and other cloud platform costs to right-size cloud expenses
- Cloud Security to continuously assess security and compliance of AWS, Azure, and other cloud platform services
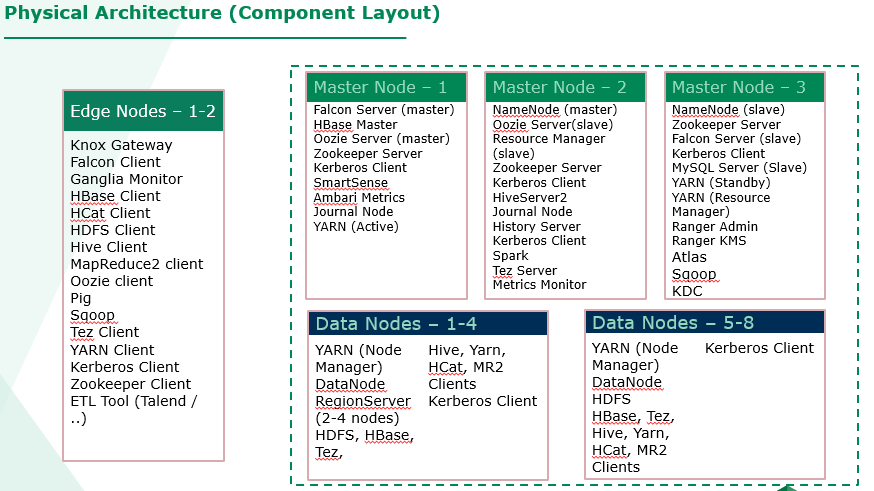
Define Your Architecture
- Putting Extra Effort in defining your architecture will help you in long run
- Before start of Production Environment, you should have a concrete plan on how to use your aggregate data
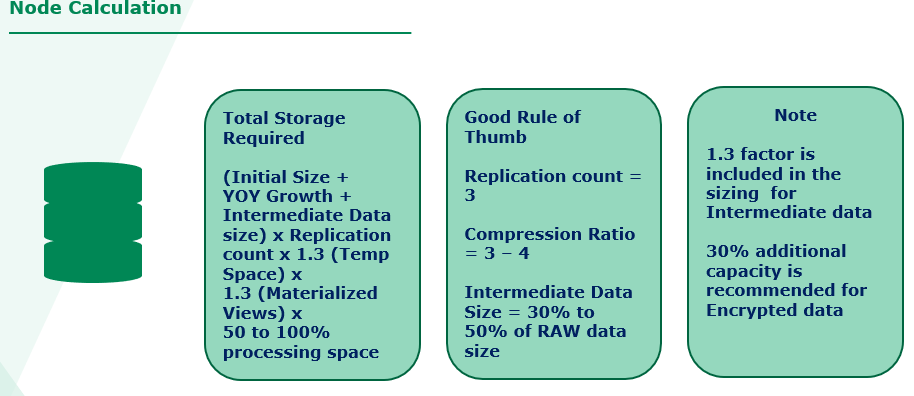
- Node Calculation
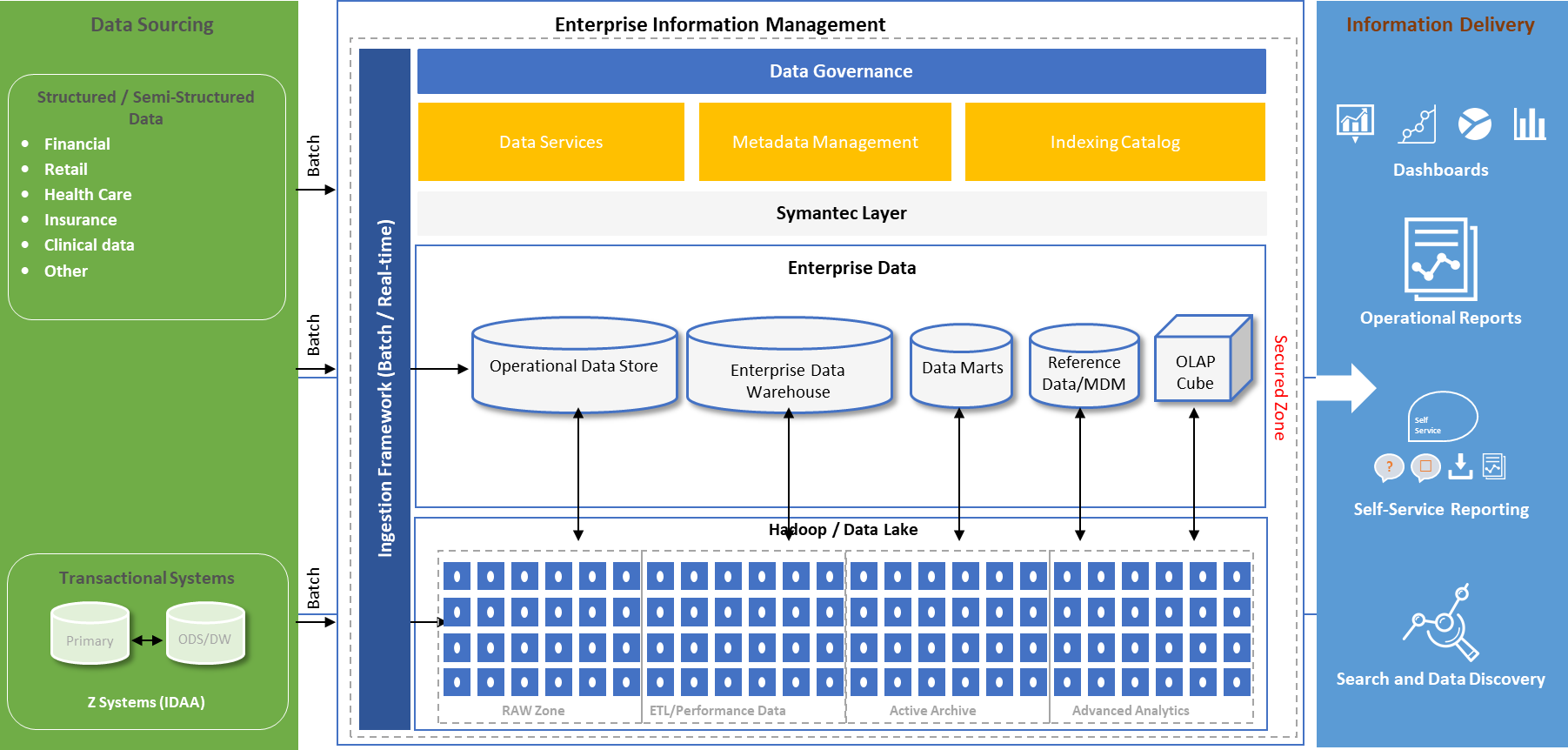
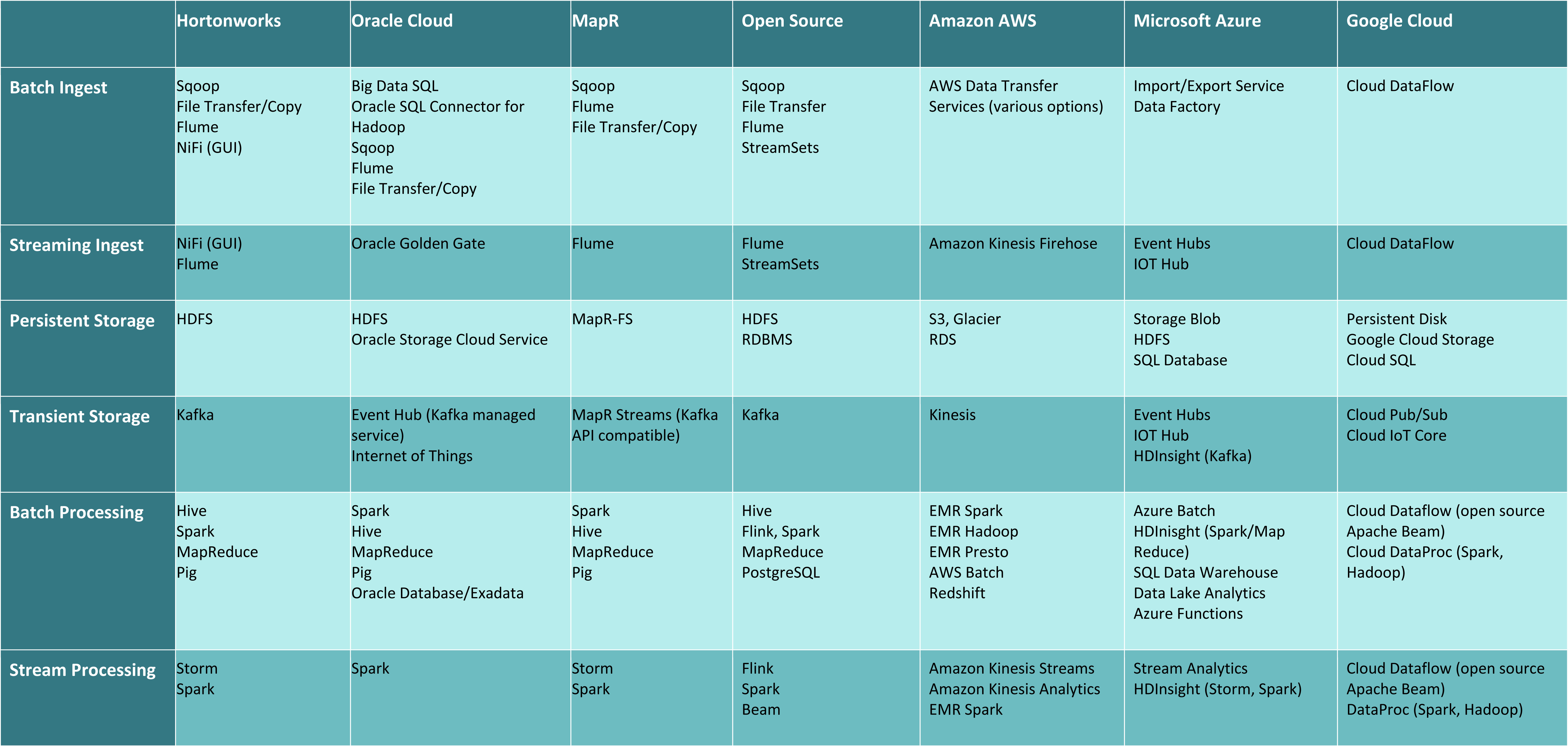
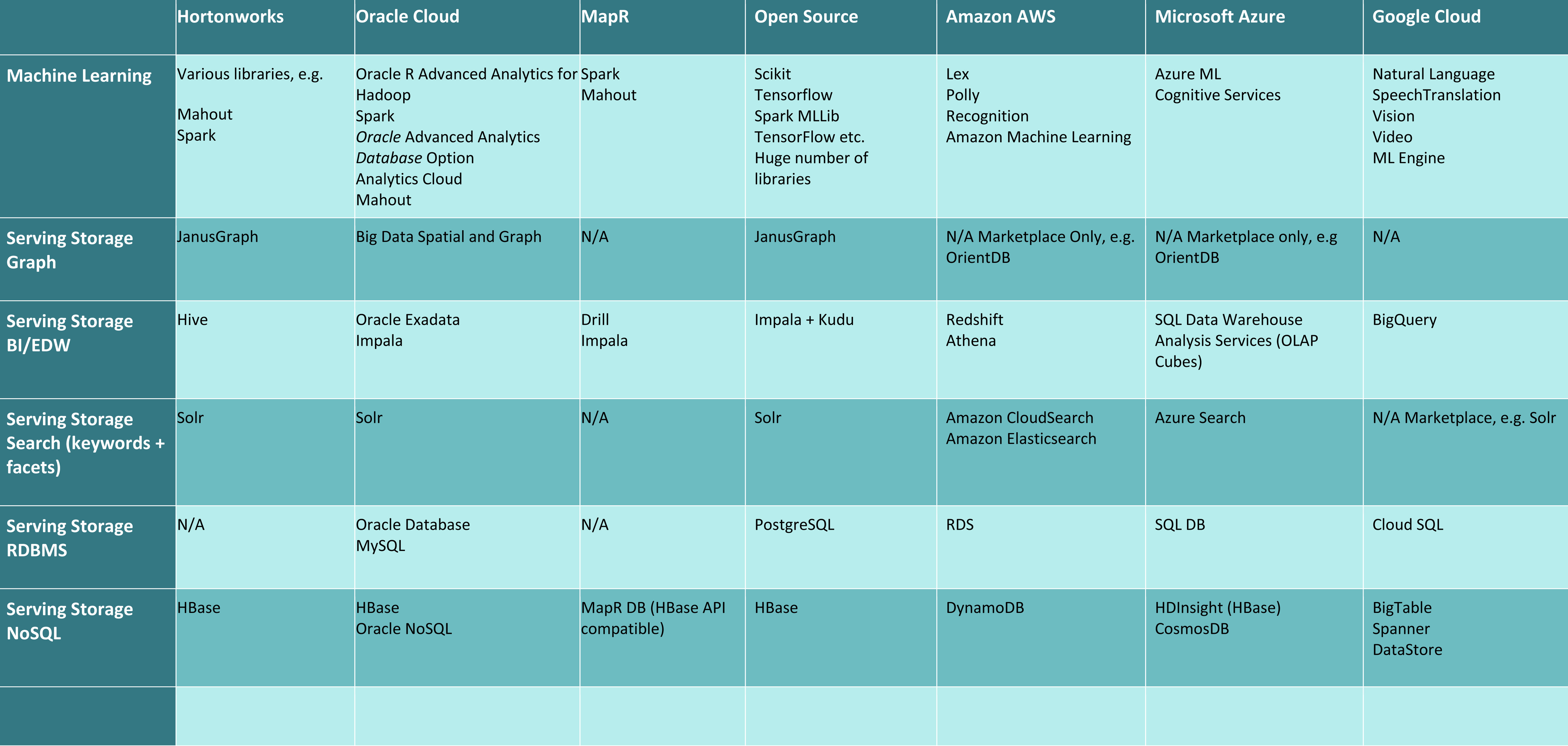
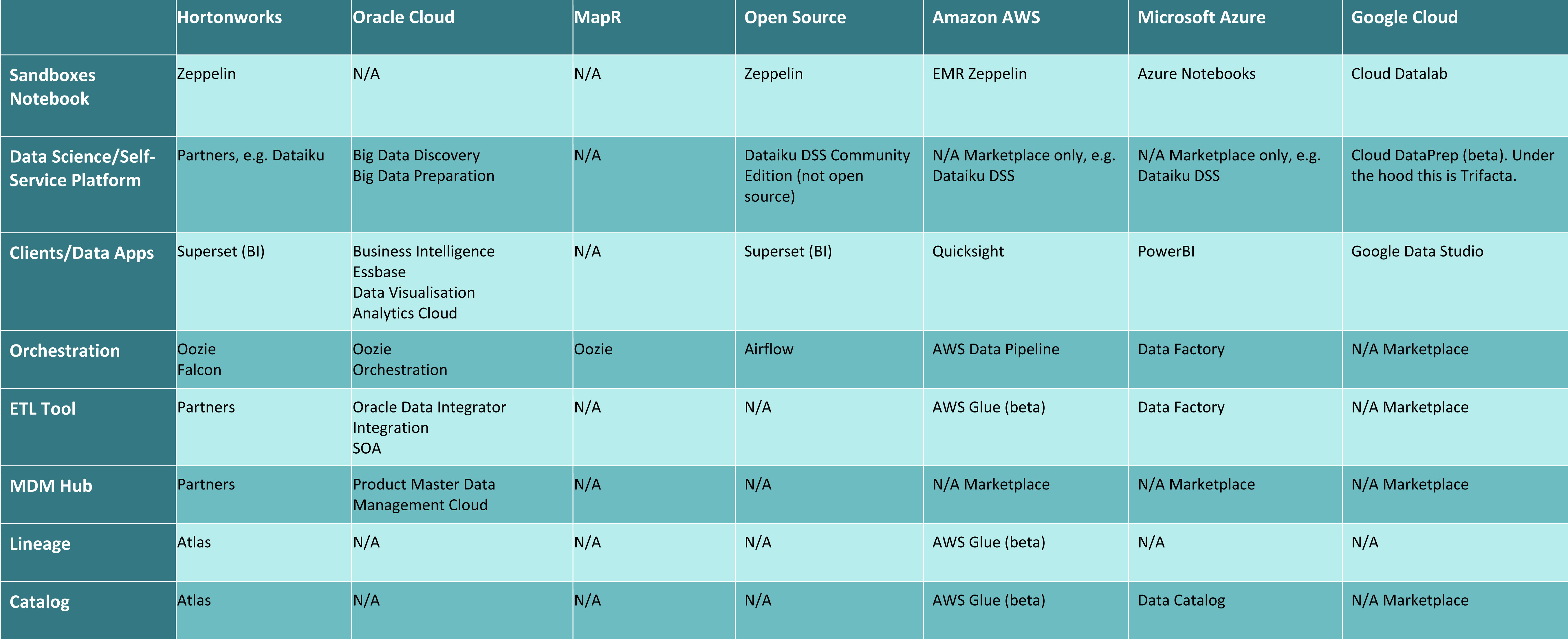
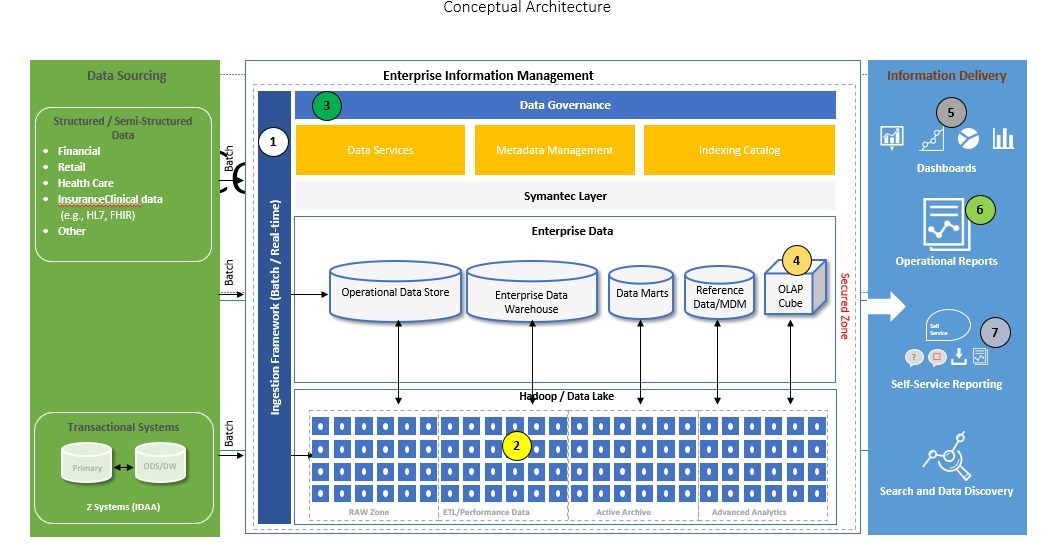
Conceptual Architecture
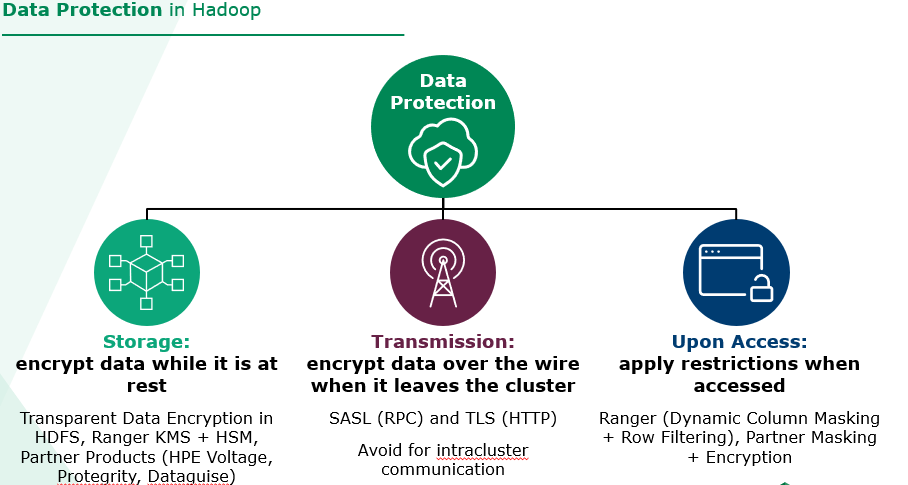
Security
- A Solid Governance Plan need to be ironed out before you setup your data lake
- Should have right security protocols in place depending on the sensitivity of your information in data lake
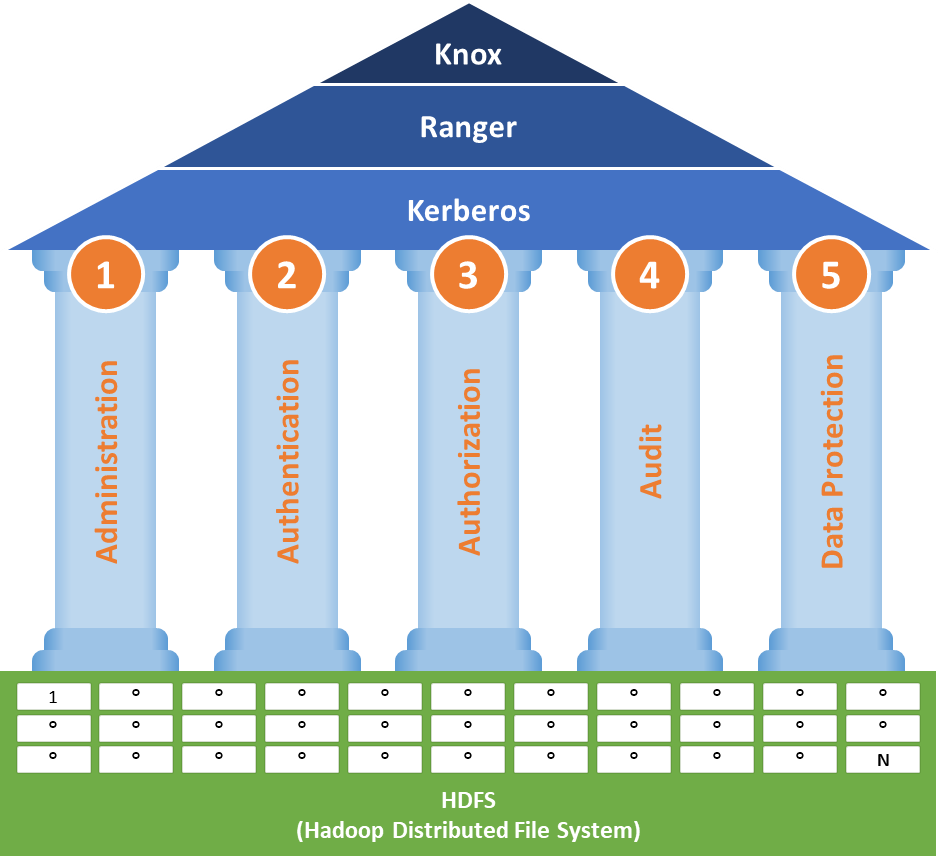
Hadoop Security Architecture Overview
Security in Hadoop is defined by 5 pillars:
Administration
Centrally Managed and consistent Security
Authentication
Authenticate users and systems
Authorization
Provision access to data
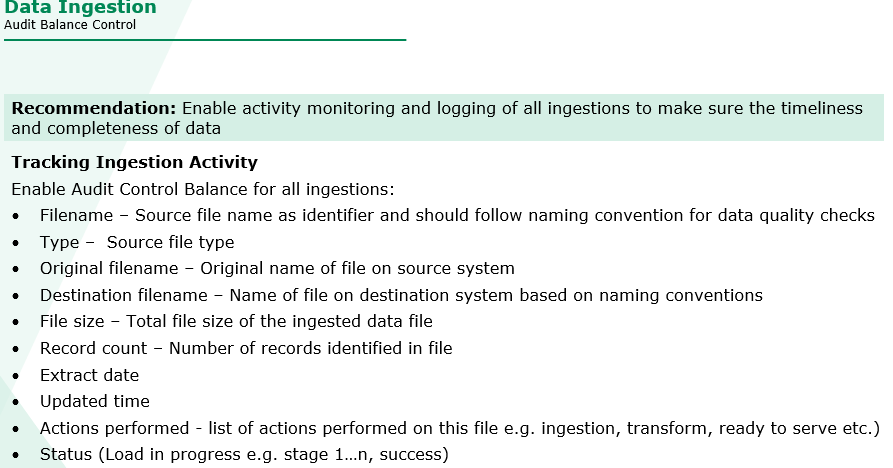
Audit
Maintain record of data access
Data Protection
Protect data at rest and in motion
Disaster Recovery
- Data Lakes can be breached or technology may fail, so disaster recovery is a must
- Plan Disaster Recovery upfront before building the data lake
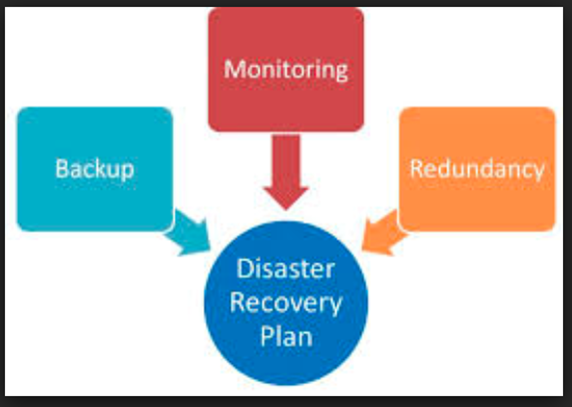
Disaster Recovery
- Minimal or no downtime for production cluster
- Ensure High Availability of HDP Services
- Ensure Backup and recovery of Databases, configurations and binaries
- No Data Loss
- Recover from hardware failure
- Recover from user error or accidental deletes
- Business Continuity
- Failover to DR cluster in case of Catastrophic failure or disaster
Future Plan
- Need to consider how your company plans on scaling in future.
- You can come up with a 3-5 year plan, which will help in future.

Future Plan
Big Data Implementations
- Real Time: Kafka/Flume Spark Streaming
- ETL Tools: Talend/Informatica/Syncsort/Pentaho etc
- Data Governance and Metadata Management: Apache Atlas/Informatica Axon
- Cached Cubes: AtScale/Druid etc
- Data Visualization: Tableau/Zoom Data
- BI Reporting: Cognos/Micro Strategy
- Data Discovery: Alteryx/Trifacta
IT Staffing
For Clients
- Ai9 Hiring Process
- Set Expectations
- Establish Relationship
- Vetting Client for Ai9 Standards
- KickOff Assignment
- Ensure Quality Standards are Maintained
- Followup and Quality Check
- Project Based Staffing
- We Provide Screened and Qualified Consultants across multiple Solutions Inc to assist with short term -long term project based work and are engaged initially to assist with the design of the client's solution and remain engaged through the completion of the project.
- Permanent Hire
- Based on the client needs we recruit resources to be placed at a client site as a full-time staff member or we assist them in converting our consultants to full time staff member

- Ai9 Core Team
- Ai9 highly talented Core Team will assist client to provide solution and help client to deal with bottle necks.

For Consultants
- Whether you're looking for a consultant position, direct hire, or working internally in our solutions and development center, our main focus, as an IT staffing agency is getting to know you so we can help you find the job that's right for you. Even if you're not looking yet, keeping in touch helps us find the right opportunity for you and the right time.
- At Ai9 we're excited about our successful partnerships between consultants and clients. We're not focused on filling open positions, but establishing relationships to find a perfect fit for you, whether you are looking for a direct hire placement or work as an IT consultant. In addition to finding that perfect fit, we will stay in touch to ensure everything is going smoothly and also get you ready for your next opportunity when the time comes.